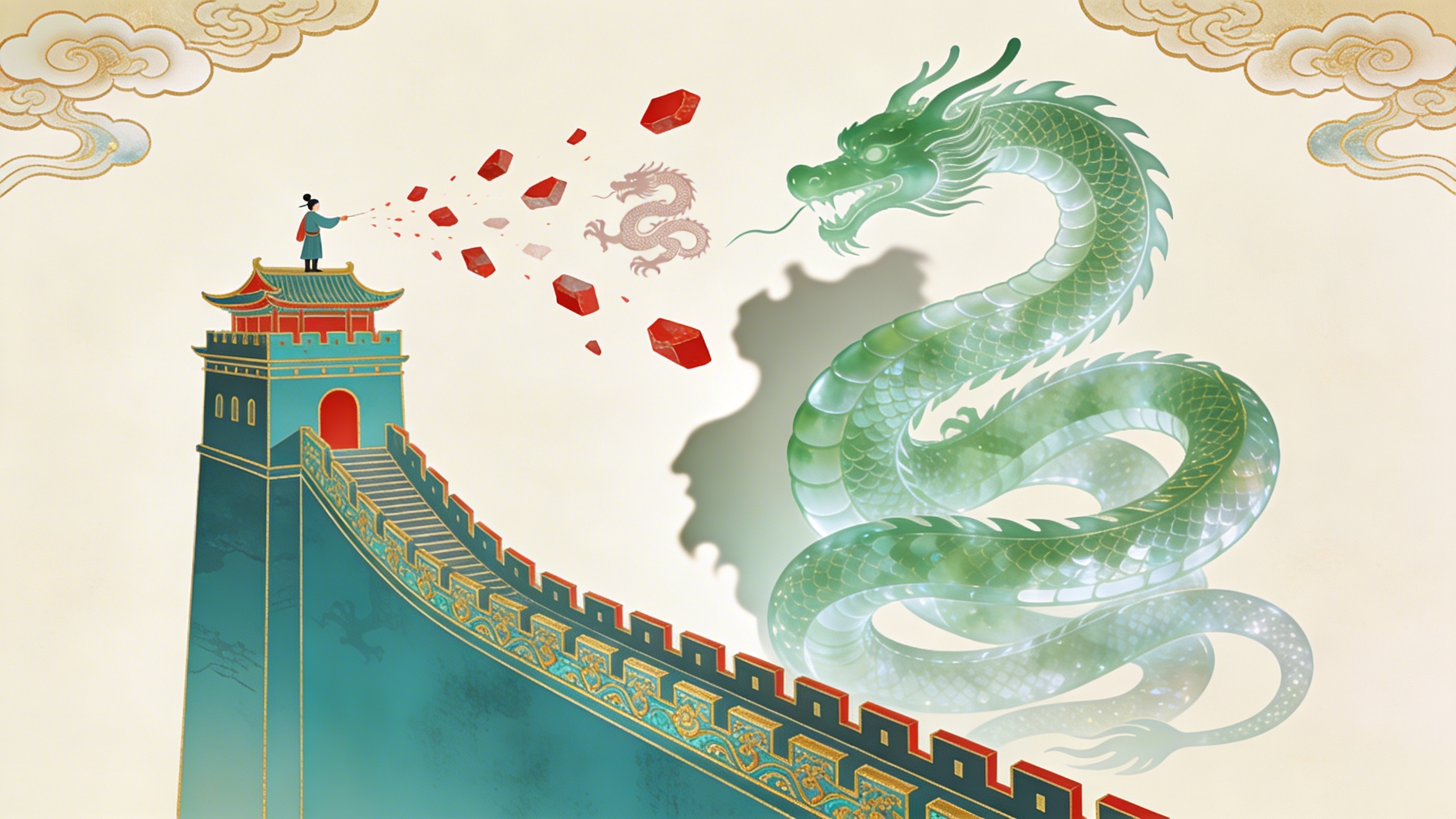
Imagine a fortress wall. The shape of the wall is built perfectly to match the shape of the specific monster the builder is terrified of. When the builder stands on the wall and throws rocks at strangers, the rocks are painted with pictures of the monster. If you want to know exactly what the builder is afraid of, don’t yell back. Just pick up a rock and look at the picture.
Simple Picture
ELI5: everyone is walking around wearing armor. The armor is not random — it is custom-fitted to protect against a specific wound. If you want to know where someone was hurt, look at where their armor is thickest. And when they attack, they attack with the weapon they fear most, because that is the weapon they understand best.
Core Claim
What we call “personality” is largely a deterministic evasion algorithm — a concealment strategy optimized not for authenticity but for the prevention of a specific, often forgotten, catastrophe.
Shame is the evolutionary hardware underneath. In ancestral environments, exile meant death. The nervous system therefore equates social exposure — being seen as deficient, deviant, or disposable — with existential threat. The polyvagal architecture is built for this: when the system detects a risk of social annihilation, it does not deliberate. It fires threat circuitry and locks the prefrontal cortex out of the conversation. The response is not a choice. It is firmware.
When a social interaction results in catastrophic status loss — being humiliated, rejected, abandoned — the system hardcodes a rule: never that again. To enforce this rule, it deploys a structural adaptation. Not a mood. Not a preference. A load-bearing identity architecture designed to control the board so the original wound never recurs. The mask is this architecture’s public face: the esteem-optimized persona that earned approval by being whatever the environment rewarded.
The Evasion Archetypes
Each archetype optimizes against a specific ancestral threat — and throws rocks painted with the monster it was built to keep out:
| Archetype | Optimizes for | To prevent | Preferred weapon |
|---|---|---|---|
| The Controller | Certainty | Surprise | ”You’re reckless” / “You have no plan” — chaos is the monster |
| The Performer | Engagement | Being forgettable | ”You’re boring” / “Nobody cares about you” — invisibility is the monster |
| The Achiever | Output | Judgment | ”You’re lazy” / “You haven’t earned it” — idleness is the monster |
| The Moralist | Virtue | Rejection | ”You’re selfish” / “You have no integrity” — moral exposure is the monster |
| The Helper | Utility | Being disposable | ”You’re useless” / “You only think of yourself” — dispensability is the monster |
| The Dominator | Spatial control | Exposure of weakness | ”You’re weak” / “You can’t handle it” — vulnerability is the monster |
| The Withdrawer | Absence | Evaluation | ”You’re too much” / “You’re embarrassing” — visibility is the monster |
The Achiever is the locally optimal structure of procrastination inverted — not avoiding work but drowning in it, for the same reason. The Helper often emerges from the ontological invalidation pattern — the child learns that the only safe form of mattering is being useful. The Withdrawer is the depressive strategy taken to its logical endpoint.
These are not character traits. They are locally-optimal strategies — designed by a frightened nervous system, frozen in time, running long after the original threat has passed. The eristics framework maps the emotional fuel: each archetype is addicted to a specific emotional argument (control, admiration, productivity, righteousness, gratitude, dominance, invisibility) and the addiction produces a recognizable rigidity when the supply is threatened.
Insults as Telemetry
Here is the sharpest diagnostic tool in the framework: hostile output is a cryptographic hash of the sender’s core vulnerability.
Insults are not objective descriptions of the target. They are high-fidelity telemetry revealing the exact boundaries of the emitter’s own identity — the specific social failure they cannot survive. shadow-formation names the projection mechanism: what you feel contempt for in others is what you are. The contempt is the shadow, unformed and unowned, erupting as judgment.
The decoding protocol:
- Capture the payload — isolate the exact insult. “Weak.” “Fake.” “Needy.” “Lazy.”
- Classify the vector — capability (“incompetent”), character (“fake”), belonging (“nobody likes you”), or control (“you’re losing it”).
- Measure the load — off-hand (mild insecurity), repeated (reinforced defense), or contemptuous (core shame). The intensity is proportional to the proximity to the wound.
- Invert to decode — the insult is the wall. The monster is its mirror.
Someone who calls you “lazy” is running a survival sentence: if I stop producing, I lose my conditional belonging and will be discarded. Someone who calls you “fake” is running: my authentic self was rejected, and I have been performing ever since. Someone who calls you “weak” is running: vulnerability was punished, and I built this armor from the material of the wound.
The self-justification engine runs on the same fuel — selectively inflating the wrongdoing of others so your own responsibility diminishes in comparison. But where resentment is defensive accounting, insults are offensive projection. Both reveal the ledger the sender cannot bear to audit.
Silence operates as telemetry too. The specific sentence a person cannot bring themselves to say reveals the wall’s shape with the same fidelity that hostile output does — which is why what goes unsaid in intimate relationships is often more diagnostic than what is said.
The Straussian Reading
The exoteric layer is a plea for empathy: everyone is fighting a hidden battle governed by evolutionary fear, so be kind.
The esoteric layer is an adversarial profiling manual. “Empathy” redefined not as emotional enmeshment but as clinical high-resolution signal intelligence. By observing the specific insults an entity emits, you bypass their defensive perimeter. Every loss of emotional regulation is an unencrypted broadcast of the sender’s entire threat architecture. You achieve territorial control of an interaction not through force but through seeing the precise matrix of fears dictating the other person’s moves.
The people-watching framework is the softer version — reading what people leak through tone, cadence, posture, and attention. Fortress walls extends it: what people attack with is even more diagnostic than what they passively leak, because attacks are involuntary revelations under pressure. The strong swimmer complicates this: a sufficiently self-aware person builds defenses sophisticated enough to survive casual inspection — but even they cannot fully control what they project under emotional load.
Common Misread
The dimwit take is “mean people are just insecure and need a hug.”
The midwit take is “we must establish psychological safety so everyone can unpack their trauma and be their authentic selves.”
The better take is that personality is an evasion algorithm optimizing against ancestral exile, and hostile outputs are inverse reflections of the sender’s localized cost function. But the worse-is-better reality must be named: assuming all aggression stems from fragile shame is itself a vulnerability. Some actors operate on pure instrumental utility or sociopathy. Treating a tiger as a traumatized housecat will get you eaten. The diagnostic formula works on people who are losing emotional regulation — it breaks against those who never had it or who weaponize it deliberately. Functional systems require friction; over-analyzing the structural shame of every participant produces paralysis. The cooler knows this instinctively — sometimes the correct response to hostility is not decoding but boundary.
Main Payoff
The fortress wall metaphor reframes social conflict from a moral event to an information event. Every insult, every defensive posture, every rigid personality pattern is data — not about the target but about the source. The wall’s shape reveals the monster. The rocks’ pictures tell you what the builder cannot say.
This does not make the rocks hurt less. But it changes what you do when hit. Instead of building your own wall higher — which only reshapes your armor around a new wound — you pick up the rock, look at the picture, and understand that the attack was never about you. It was always about the shape of someone else’s fortress. The anatomy of conflict extends this from individual personality to interpersonal dynamics: fights escalate not because the disagreement is intractable but because threat has been activated — and the fortress wall is what makes the activation hair-trigger.
The deepest version: your own fortress follows the same architecture. The insults you reach for under pressure, the personality patterns you cannot put down, the contempt that feels like clarity — all of it is painted with pictures of your own monster. Self-acceptance begins not with accepting yourself but with reading your own walls honestly enough to recognize what they were built to hide. Empowered dialogue operationalizes the same read in live conflict: your wall is data you can use in real time — when listening fails and you feel the old defensiveness clench, back up to the wall and ask what it is guarding, which is often the exact piece of self-knowledge you needed in order to let the other person in. Orphaned independence is the specific wall pattern where the monster being kept out is the possibility of being revised by anyone — the self-reliance variant whose favored insults (you’re clingy, you’re needy, you’re too much) all decode to the same wound: every person who once tried to count was too painful to let count again.